Zero Trust for Remote Scrum Teams: Beyond the VPN
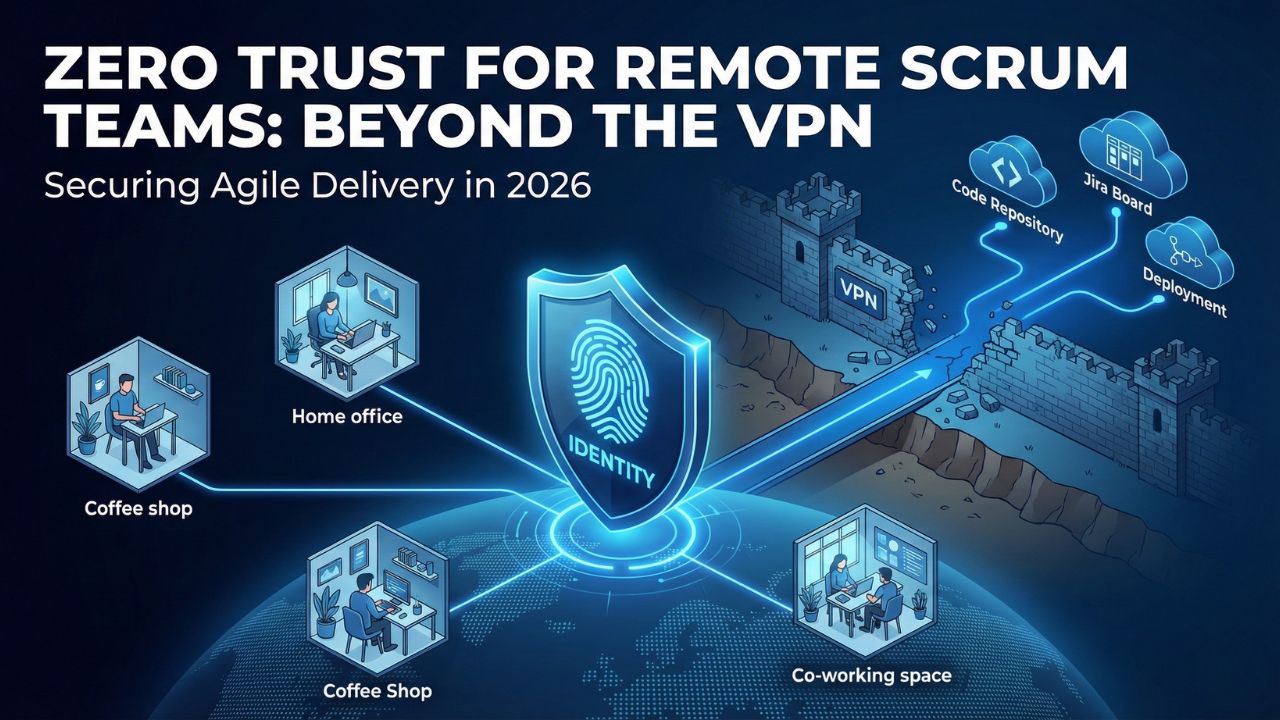
For decades, corporate security relied on the "Castle and Moat" model. You built a strong firewall (the moat) around your office (the castle). If a developer was inside the building or connected via VPN, they were trusted.
In 2026, this model is dead. Agile teams are distributed globally, accessing cloud resources from coffee shops, home offices, and coworking spaces. The "perimeter" is no longer a physical location; it is everywhere your developers are.
Relying on a VPN for a distributed Scrum team is not just a security risk; it is a velocity killer. VPNs create bottlenecks, latency, and a single point of failure. If an attacker steals one VPN credential, they have the keys to the entire castle.
This guide explores Zero Trust Architecture (ZTA), the modern security standard where identity is the new firewall. We will explore how to move beyond the VPN and implement least privilege access principles in DevOps.
1. The Core Principle: Never Trust, Always Verify
Zero Trust is not a product; it is a mindset. The core mantra is simple: "Never Trust, Always Verify."
In a traditional network, once you login, you can move laterally to different servers. In a Zero Trust architecture for remote teams, every single request, whether it’s to pull code from Git, access a Jira ticket, or deploy a container—is treated as if it originated from an open network.
The Three Pillars of Zero Trust for Agile:
- Verify Explicitly: Always authenticate and authorize based on all available data points (user identity, location, device health).
- Use Least Privilege Access: Developers should only have access to the specific microservices or repositories they need for this Sprint, not the entire codebase. This aligns with Automated Compliance & Governance standards.
- Assume Breach: Design your network as if an attacker is already inside. Minimizing the "blast radius" prevents a compromised laptop from taking down production.
2. Identity Access Management (IAM): The New Firewall
If the network doesn't matter, what does? Identity.
Identity and Access Management (IAM) is the control plane of Zero Trust. For a Scrum team, your IAM solution acts as the bouncer for every digital door. It ensures that the person trying to merge code is actually who they say they are.
This is where the highest-value tools in the industry come into play. Modern IAM solutions integrate Multi-Factor Authentication (MFA) directly into the developer workflow. This is crucial for teams managing AI-generated code security as well.
- Adaptive MFA: Instead of asking for a code every time, the system analyzes risk. Login from a new country? Ask for a fingerprint. Login from the usual laptop? Allow pass-through.
- Single Sign-On (SSO): One strong identity allows access to Jira, GitHub, AWS, and Slack, reducing password fatigue and the risk of weak credentials.
3. Zero Trust vs. VPN: Why Developers Hate VPNs
The transition from VPN to Zero Trust Network Access (ZTNA) is one of the biggest quality-of-life upgrades for an engineering team.
| Feature | Traditional VPN | Zero Trust Network Access (ZTNA) |
|---|---|---|
| Access Level | Network-level access (User gets an IP on the internal network). | Application-level access (User connects only to specific apps). |
| User Experience | Slow connection times, frequent disconnects, "backhauling" traffic. | Direct-to-cloud connection, fast and seamless. |
| Security Risk | High. Lateral movement is easy if breached. | Low. Application is cloaked; lateral movement is blocked. |
| Scalability | Difficult to scale hardware concentrators. | Cloud-native and infinitely scalable. |
Agile Action: Replace your VPN client with a ZTNA agent. This allows developers to access the specific cloud environments they need without exposing the entire backend network.
4. Top 5 Identity & Zero Trust Tools for 2026
To secure a distributed agile team, you need a stack that handles Identity (Who are you?), Device Health (Is your laptop clean?), and Access (What can you touch?).
- Okta: The industry leader in IAM and SSO. High bids for "Identity Management."
- Ping Identity: Specialized in enterprise-grade identity security and API intelligence.
- Zscaler: A leader in ZTNA, replacing traditional firewalls and VPNs with a cloud-native exchange.
- Duo Security (Cisco): The standard for user-friendly Multi-Factor Authentication (MFA).
- Cloudflare Access: A great "BeyondCorp" style solution accessible for small businesses and startups.
5. The Maturity Model: How to Start
You cannot buy "Zero Trust" in a box. It is a journey. Use the CISA Zero Trust Maturity Model to benchmark your Scrum team:
- Stage 1 (Traditional): Manual password management, heavy reliance on VPNs.
- Stage 2 (Advanced): MFA implemented everywhere, some segmentation of the network.
- Stage 3 (Optimal): Fully automated IAM, continuous validation of device health, and dynamic "Just-in-Time" access grants for production deployments.
FAQ: Zero Trust for Agile Teams
Q: Does Zero Trust mean we don't trust our own employees?
A: No. It means we don't trust the connection or the device implicitly. It protects the employee by ensuring that if their credentials are stolen, the attacker cannot access sensitive systems.
Q: Is Zero Trust expensive to implement for small teams?
A: It can be, but tools like Cloudflare Access or Google BeyondCorp offer free or low-cost tiers for small businesses to start replacing VPNs.
Q: How does Zero Trust impact velocity?
A: Initially, there is a setup curve. However, once implemented, ZTNA is often much faster than a VPN, removing latency and connection hurdles, effectively increasing velocity.
Q: What is ZTNA?
A: ZTNA stands for Zero Trust Network Access. It is a technology that creates a secure connection to a specific application based on access control policies, denying access to the rest of the network.
Sources and References
-
[cite_start]
- NIST – Zero Trust Architecture (SP 800-207) [cite: 189] [cite_start]
- CISA – Zero Trust Maturity Model Version 2.0 [cite: 198]
- Forrester – The Zero Trust eXtended Ecosystem
- Google Cloud – BeyondCorp: A New Approach to Enterprise Security
- Scrum Day India – DevSecOps 2026: The Guide to Secure Agile Delivery (Return to Pillar Page)